Windows Server 2016 has reached the General Availability (GA) milestone today. You can download it from your volume licensing site or MSDN. You can also create Azure VMs with Windows 2016.
The latest and greatest Windows Server has many new Remote Desktop features. See What’s New in Remote Desktop Services in Windows Server 2016 for the laundry list.
If you’re just trying to enable RDP for remote admin connections, here’s how to do it.
- Type SystemPropertiesRemote.exe in a command or PowerShell window.
- In the System Properties dialog, select Allow remote connections to this computer.
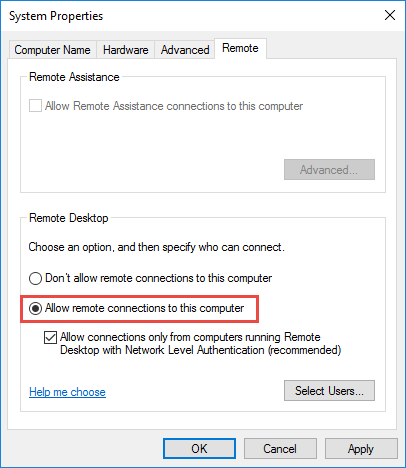
Figure 2: Allow remote desktop connections.Windows Server supports Network Level Authentication (NLA) for RDP connections. This forces the authentication to occur before the session begins. Without NLA, the RDP host presents the user logon screen when the RDP session starts. NLA is more secure.
- [Optional] Administrators have remote desktop access by default. If you want to allow RDP access to additional users, click Select users, select the users and then close the dialog box.
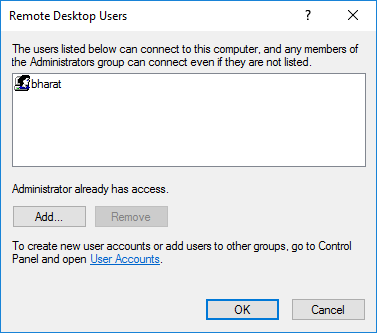
Figure 3: Select users who should be allowed remote desktop connections
Enable Remote Desktop using PowerShell
Of course, many IT pros prefer PowerShell. In this case, I found running SystemPropertiesRemote.exe was faster, but PowerShell helps you automate these settings, for example, as part of unattended setup.
Here’s how you can enable Remote Desktop using PowerShell (credit to Samuel Yee, who has it documented here, saving me the trouble to fire up Process Monitor, one of the fine, and free, Windows SysInternals tools):
- Enable Remote Desktop connections
Set-ItemProperty ‘HKLM:\SYSTEM\CurrentControlSet\Control\Terminal Server\‘ -Name “fDenyTSConnections” -Value 0
- Enable Network Level Authentication
Set-ItemProperty ‘HKLM:\SYSTEM\CurrentControlSet\Control\Terminal Server\WinStations\RDP-Tcp\‘ -Name “UserAuthentication” -Value 1
- Enable Windows firewall rules to allow incoming RDP
Enable-NetFirewallRule -DisplayGroup “Remote Desktop”
There are scripts in the TechNet Script Gallery that’ll allow you to run this against a large number of computers and turn on any services required to automate this.
Update 12/13/2018:
You can use PowerShell to grant permissions to use Remote Desktop. As noted earlier in this post, administrators can remote in by default. To provide non-admin users permission to use Remote Desktop, add them to the Remote Desktop Users local group.
Add-LocalGroupMember -Group "Remote Desktop Users" -Member foo

{ 6 comments… read them below or add one }
Hi Team,
The Article is nice. I got my required info.
If I want add user to remote desktop (Like you added bharat in third step) through powershell may i know what is option.
Thanks
Samba
Admins can RDP by default. To provide non-admin users to use Remote Desktop, add them to the Remote Desktop Users local group.
Add-LocalGroupMember -Group "Remote Desktop Users" -Member foocan a variable be used to add the “-Member” flag – e.g.
Add-LocalGroupMember -Group “Remote Desktop Users” -Member %user%
No, but you can use variables in PowerShell. What are you trying to accomplish with %user%? Add the current user?
You can always try out these things on a test box or VM.
Great article explaining remote desktop connections for Admins on Windows Server 2016. But just I wanted to know, instead of above, wouldn`t be easy for admins to remotely connect to Windows Server 2016 using tools like logmein, R-HUB remote support servers etc?
Thank you so much for this! It solved this problem that I had been stuck with for almost 1 month.
Really appreciate!