If you haven’t looked at Palo Alto-based cc:Betty yet, perhaps you should. cc:Betty promises to keep everyone on the same page. Still in beta, it’s a useful web app that helps users organize their email communication, collects email content, catalogs attachments and files, and also maintains your contacts.
It’s also amazingly simple to use. Besides adding content on the cc:Betty web site, users can simply add [email protected] as an additional recipient (To/Cc/Bcc) to email they send, and it shows up in their cc:Betty account – email content, attachments, et al. With the click of a button, users can publish the discussion to their Facebook feed.
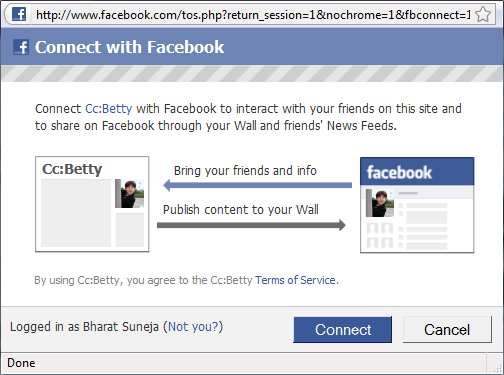
Figure 1:With the click of a button, cc:Betty posts your discussion to your Facebook profile
And therein lies the threat to your data!
Although it’s an impressive tool for personal use (the usual caveats about personal information and privacy apply), organizations and IT departments must consider the consequences carefully. Many small businesses and organizations operating in unregulated industries or locales may not consider themselves to be at risk and actually welcome such services.
If your organization isn’t one of them, consider that simply adding another recipient to all email messages results in data leakage. How’s this any different from adding any other recipient to an email? Unlike other recipients, the sole purpose of cc:Betty is to facilitate further sharing of email content outside an organization. Email can contain sensitive information— including high business impact (HBI) data or personally identifiable information (PII). Transmitting and storing such information outside the organization, with no control over the content or its security, could expose your organization to multiple risks.
It’s important to consider what services such as cc:Betty do with your information. cc:Betty’s privacy policy is not very different from Gmail’s privacy policy— email content is scanned to display relevant ads. Some would argue that similar content scanning is also performed by antispam and antivirus software and services, and that this isn’t something to be concerned about.
Regardless of whether you find content scanning by an automated process acceptable or not, the bigger threat is data leakage.
If usage of cc:Betty and other such services is in violation of your organization’s policies, your users must be informed. If your organization’s policies don’t address such services and usage, perhaps it’s time to consider a policy review. You may also want to consider blocking outbound mail to domains offering such services.You can easily block outbound mail to a domain using transport rules or a Send Connector. Exchange 2010’s Information Rights Management (IRM) features can also help you prevent data leakage.
What can cc:Betty do to help organizations?
How can cc:Betty help organizations protect themselves from unauthorized use of its service? As a web-based service its success lies in widespread adoption of its app. More users, more user content accumulated, more sticky the service proves to be, and more pageviews it racks up. As such, there’s no incentive to actually stop users from joining or posting information. In fact, it may directly impact its success.
However, cc:Betty and other such services may gain a lot of goodwill and more acceptance if they work with organizations to help prevent data leakage. One way of doing this may be to block email from organizations that register with it. When a user signs up for an account using your organization’s email address, he/she gets a polite message about your company not allowing use of the service. Email sent from your domain can also be bounced back with a polite NDR.
Some organizations may choose to allow their users to use the service, but with appropriate policy guidelines and controls in place. [Update: According to cc:Betty, an enterprise version of the service is in the works.]
Does your organization allow the use of cc:Betty.com or similar services?

{ 3 comments… read them below or add one }
So you raise the flag, then pull excerpts from the privacy policy, and then…
you find nothing wrong with the privacy policy, finding it to be like Gmail? The takeaway? If you let people in your org send email to any user on gmail, you should be fine letting them Cc:Betty.
Reading this was 2 minutes of my day i'll never get back. Maybe I'll write a blog post about how to block my employees from reading this blog.
@Rick: The takeaway as far as privacy policy comparison is – if your users use services such as Gmail and your organization doesn't have any issues with it, you should be fine with cc:Betty.
If compliance is important, you may want to address usage of such services – in your policy and implementation.
I think that compliance is key to every implementation that we have. The threat is not really the data scanning but the leakage of information. Not all users have our mindset.